

“They really know what they need,” and are putting “serious effort” into acquiring advanced machine tools, factory equipment, research and dual-use technology, said Christoffer Wedelin, deputy head of operations at the Swedish Security Service.
Russia also needs sanctioned computer technology and software updates for machine tools, Martelius said.
Even more important to the KGB was obtaining research data about Western technology, including integrated circuit design, computer-aided manufacturing, and, especially, operating system software that was under U.S. export control. They offered 250,000 Deutschmarks for copies of Digital Equipment’s VMS operating system.
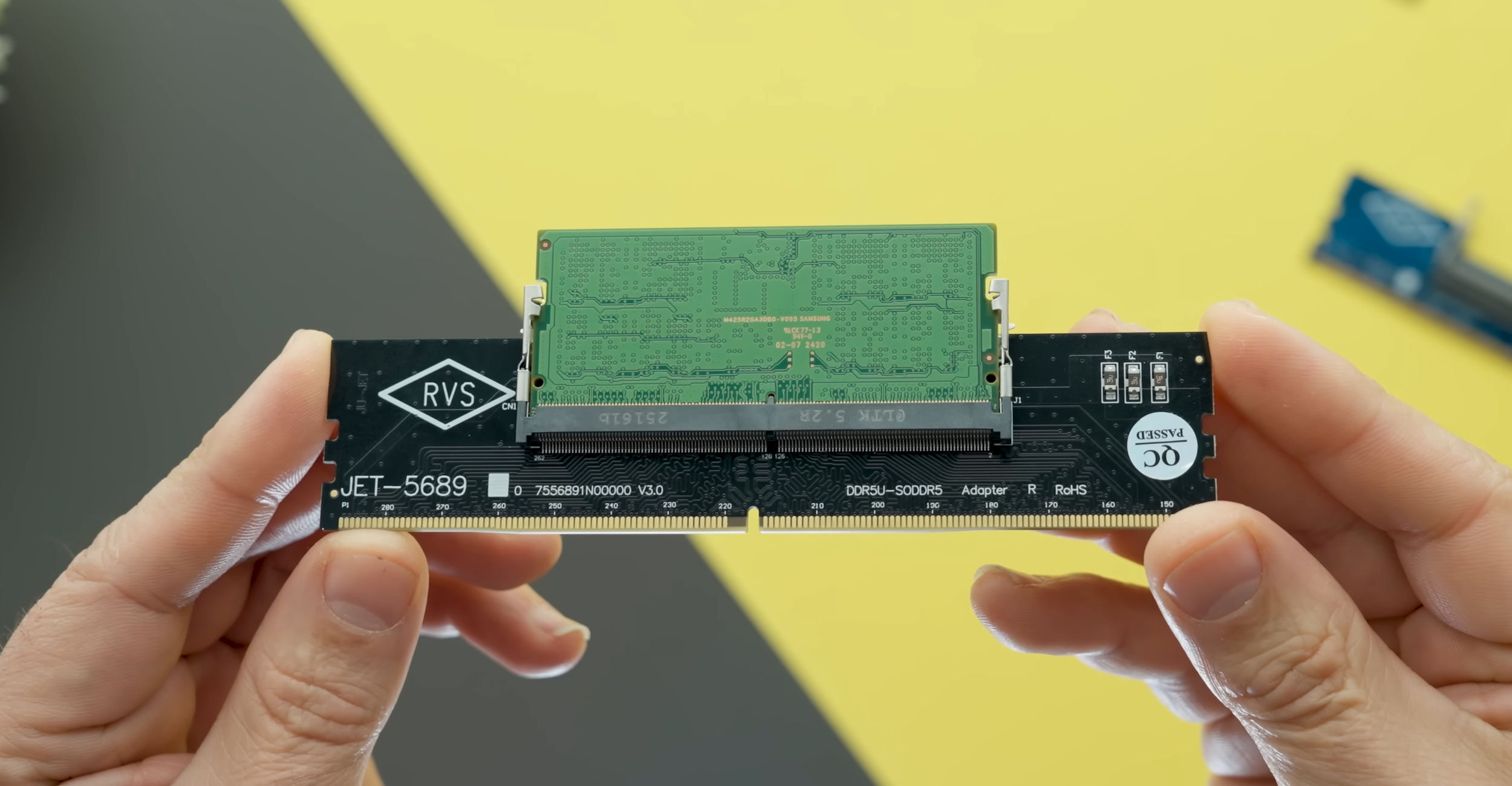
Peter Carl and Dirk Brezinski apparently met with the KGB a dozen times, filling many of their requests: source code to the Unix operating system, designs for high-speed gallium-arsenide integrated circuits, and computer programs used to engineer computer memory chips.
Alone, the source code to Unix isn’t worth $130,000. Chip designs? Perhaps. But a sophisticated computer design program . . . well, maybe the KGB did get its money’s worth.
— The Cuckoo’s Egg, discussing the situation in 1986
That was 40 years back and when the Soviet Union was still around. Some things haven’t changed all that much.



















https://www.espn.com/soccer/story/_/id/48707727/fifa-triples-best-available-world-cup-final-ticket-33k
More expensive than for NFL tickets!
https://www.usatoday.com/story/sports/nfl/super-bowl/2026/01/21/super-bowl-60-ticket-prices-purchase-cheapest/88274794007/